Smart locks and access systems use electronic credentials and software to control entry. They verify permissions in real time and log events for accountability. The approach blends security with convenience, while introducing privacy and vulnerability considerations if defenses are weak. Evaluating use cases, infrastructure, and privacy factors is essential. Deployment requires standardized testing, clear governance, and proactive maintenance. The balance between protection and practicality invites careful examination of implementation choices and their long-term consequences.
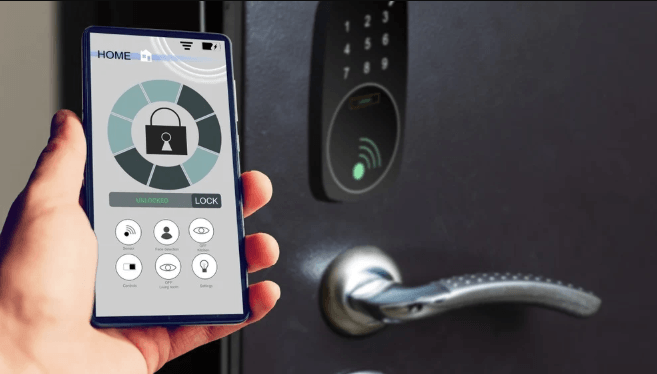
What Are Smart Locks and Access Systems?
Smart locks and access systems are electronic mechanisms and software that control entry to a space without relying on traditional mechanical keys. These systems analyze credentials, grant or deny access, and log events for accountability. They introduce security vulnerabilities if defenses are weak, and raise concerns about user privacy through data collection, while offering traceable, flexible control for authorized individuals seeking freedom within limits.
How They Improve Security and Convenience
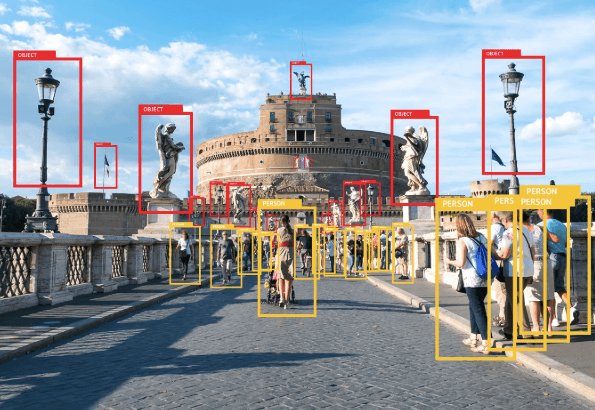
Access control is enhanced through real-time credential verification, ambient monitoring, and rapid revision of permissions, which together reduce unauthorized entry and enable timely responses to incidents.
The result is measured improvement in operational security and user convenience, with streamlined access logs and audit trails.
However, security breaches and privacy concerns require ongoing assessment to balance openness with protective controls and user autonomy.
Choosing the Right System for Your Space
Choosing the Right System for Your Space requires a structured evaluation of use cases, risk tolerance, and operational priorities. A methodical comparison weighs integration with existing infrastructure, scalability, and user management. Privacy concerns guide data handling and auditability, while power management informs reliability and maintenance rhythms. Selection should balance control granularity with resilience, ensuring secure access without sacrificing user autonomy.
Best Practices for Deployment, Use, and Maintenance
Effective deployment, use, and maintenance of smart locks and access systems require a structured, data-driven approach that prioritizes reliability, security, and operational continuity.
The analysis focuses on standardized rollout, rigorous testing, and clear responsibility matrices.
Emphasis on privacy compliance, secure update practices, and battery longevity informs ongoing monitoring, predictive maintenance, and incident response, enabling sustained freedom with minimal vulnerability.
Continuous evaluation supports resilient access governance.
Frequently Asked Questions
How Do Smart Locks Handle Power Outages and Battery Failures?
During power outages, smart locks rely on backup power management and battery health monitoring to maintain access; devices switch to reserve power, log events, and alert users when battery capacity declines, ensuring controlled entry while preventing unauthorized bypass.
Are Smart Locks Compatible With Legacy Door Hardware and Wiring?
Yes, most smart locks support legacy compatibility via standard mortise and cylindrical hardware, though compatibility varies by model; a wiring retrofit may be required to integrate power, sensors, and latching mechanisms in older doors.
What Are the Legal and Privacy Implications of Access Data?
The legal and privacy implications of access data involve legal data storage, privacy consent, security compliance, and data minimization; institutions balance obligations with user autonomy, ensuring transparent governance, robust safeguards, and proportional collection to respect freedom while mitigating risk.
Can Smart Locks Be Audited for Security Vulnerabilities and Firmware Updates?
Lightning flashes reveal a silver truth: yes, they can be audited for security vulnerabilities and firmware updates. Security auditing and firmware updates are methodically applied, with precise analysis, documenting findings, risk prioritization, and transparent remediation for autonomy-minded users.
See also: Smart Lighting Systems Explained
How Do I Recover Access if the Smartphone Is Lost or Stolen?
In case of a lost or stolen smartphone, recovery procedures emphasize removing device access, reconfiguring credentials, and notifying administrators; follow established lost device protocols to regain entry while preserving security. The procedure remains methodical, analytical, and user-empowered.
Conclusion
Smart locks and access systems offer streamlined control, real-time verification, and activity logging that bolster security and convenience. They enable rapid credential updates and remote governance while reducing reliance on physical keys. However, they introduce privacy considerations and potential vulnerabilities if defenses are weak. Effective deployment hinges on standardized testing, clear governance, proactive maintenance, and robust incident response. When implemented thoughtfully, these systems function like a precise, well-tortured lock—keeping access restricted yet readily verifiable for authorized users.